#
App Registration
02 Nov 2023
Please make sure to have completed the steps in the previous section.
#
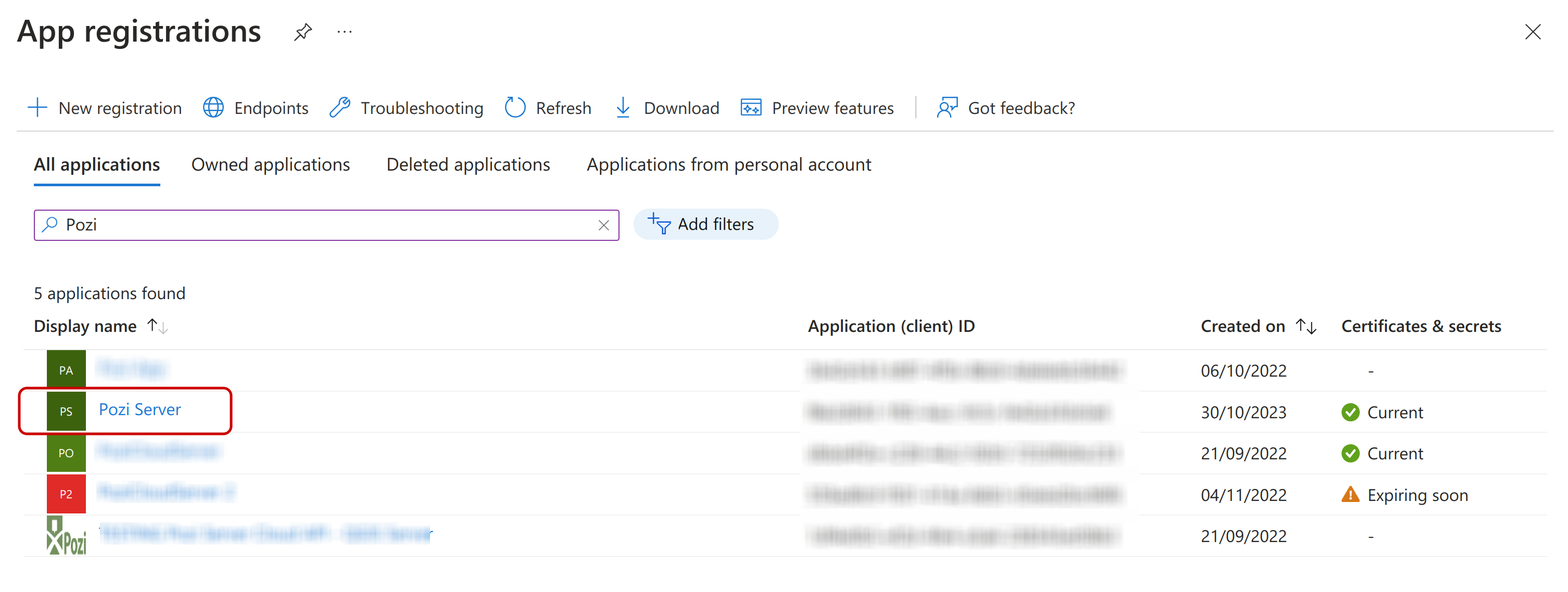
1. Configure Pozi Server Application registration
The creation of the Pozi Server Enterprise Application has also implicitly created an app registration with the same name. Search for this app in the 'App registrations' section in Entra ID.
#
2. Authentication
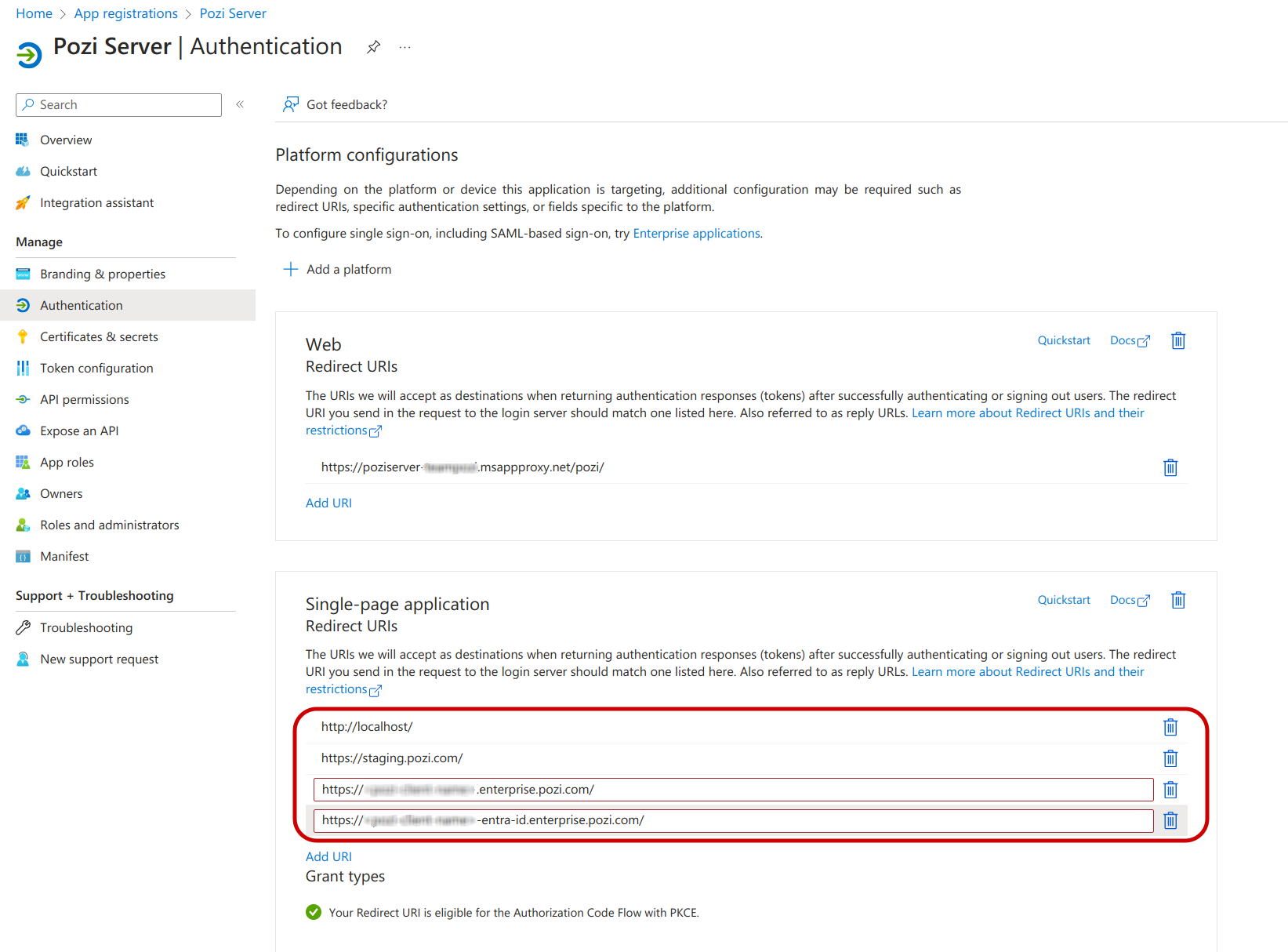
In this section we will make sure that an authenticated user will be granted access through the Pozi Web App.
First, confirm that one Redirect URI has been configured that points to the Application Proxy URL that we have configured in the previous section. If it's not there, please add now.

Now, add a platform and choose 'Single-page application'. It will ask to fill in a Redirect URI. Fill in http://localhost/. We will add a few more in the next step.

Add the missing Redirect URIs from the list below in the Single-page application section:
http://localhost/(for Pozi development purposes)https://staging.pozi.com/(for client testing/debugging)https://<pozi-site-name>.enterprise.pozi.com/(replace<pozi-site-name>with the actual site name)https://<pozi-site-name>-entra-id.enterprise.pozi.com/(optional: only for clients that transition their existing site to Entra ID)
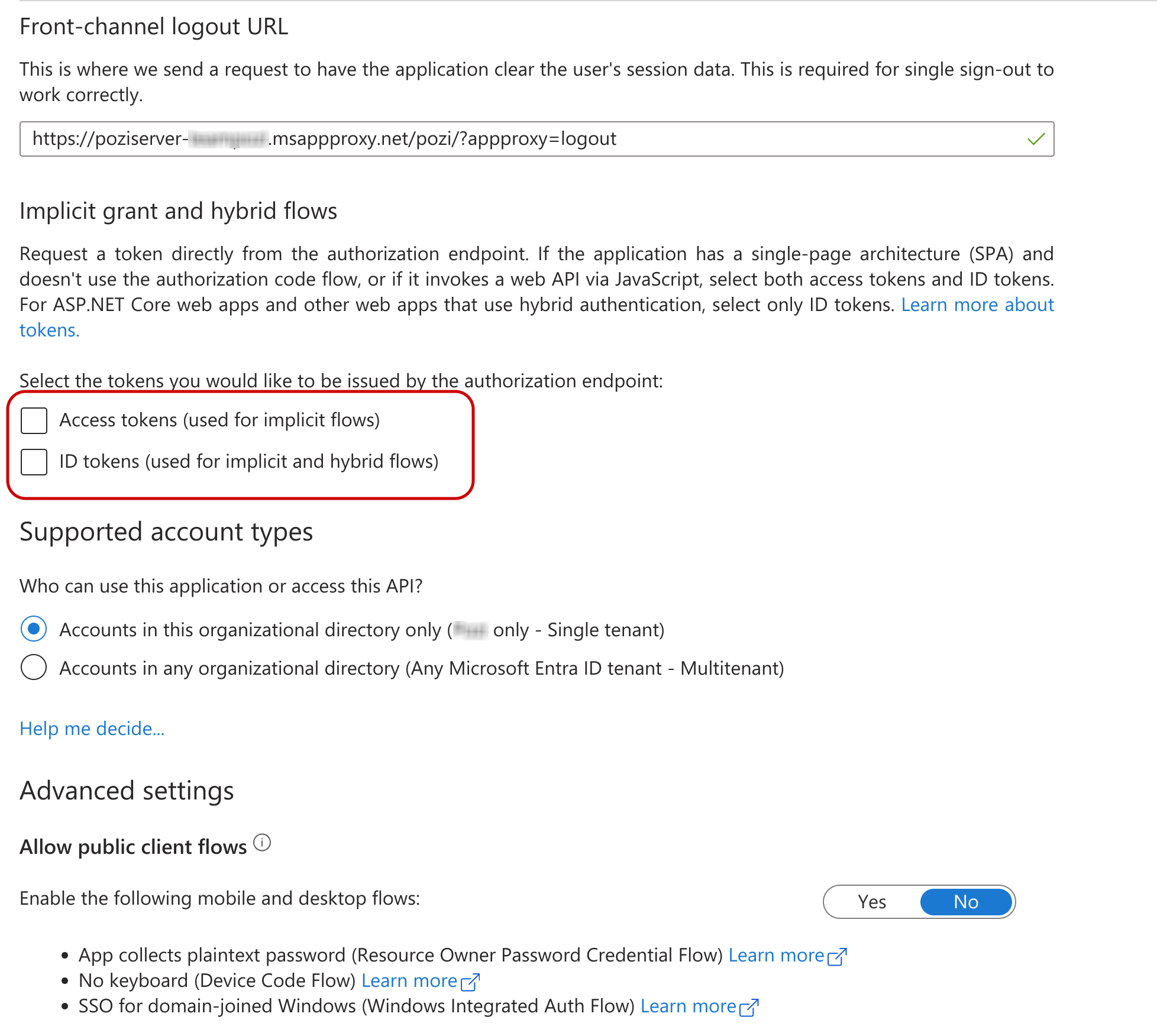
There are some more settings in this section. Most can be ignored. Confirm that the following have the values below.
- Access tokens: Unchecked
- ID tokens: Unchecked
- Enable the following mobile and desktop flows:
No
#
3. Expose an API (user_impersonation)
This section covers a crucial setting for the application to access Pozi Server on behalf of the user: the user_impersonation scope.
Go to the 'Expose an API' section of Pozi Server.
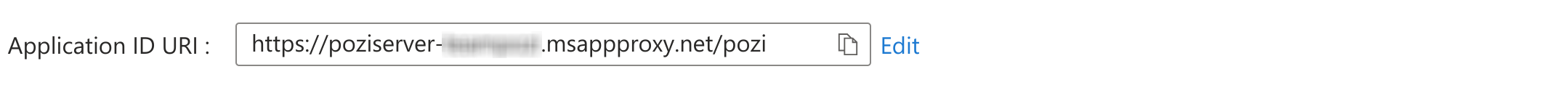
Firstly, confirm that the Application ID URI looks something like https://poziserver-<entra-application-client-name>.msappproxy.net/pozi. This should not be changed.
Make sure that in the 'Expose an API' section there is one scope defined, called user_impersonation (prefixed by the Application ID URI above).
Often, this scope gets created by Entra ID automatically but not in every organisation. If this scope is missing, add it as following.

- Scope name:
user_impersonation(correct spelling is crucial!) - Who can consent?:
Admins only - Admin consent display name:
Access Pozi Server - Admin consent description:
Allow the application to access Pozi Server on behalf of the signed-in user. - User consent display name:
Access Pozi Server(optional) - User consent description:
Allow the application to access Pozi Server on your behalf.(optional) - State:
Enabled

The scope above will be used in the Site Configuration in Pozi in the 'Scopes' section. It should look something like:
https://poziserver-<entra-application-client-name>.msappproxy.net/pozi/user_impersonation
#
4. Access control
It is possible to further control user access to map catalogues (ie QGIS projects) in Pozi Web App. In order to enforce this access control, Pozi Web App needs to know what groups a user is a member of in the Entra ID environment is required.
This section describes how to provide Pozi Web App with the relevant group information.
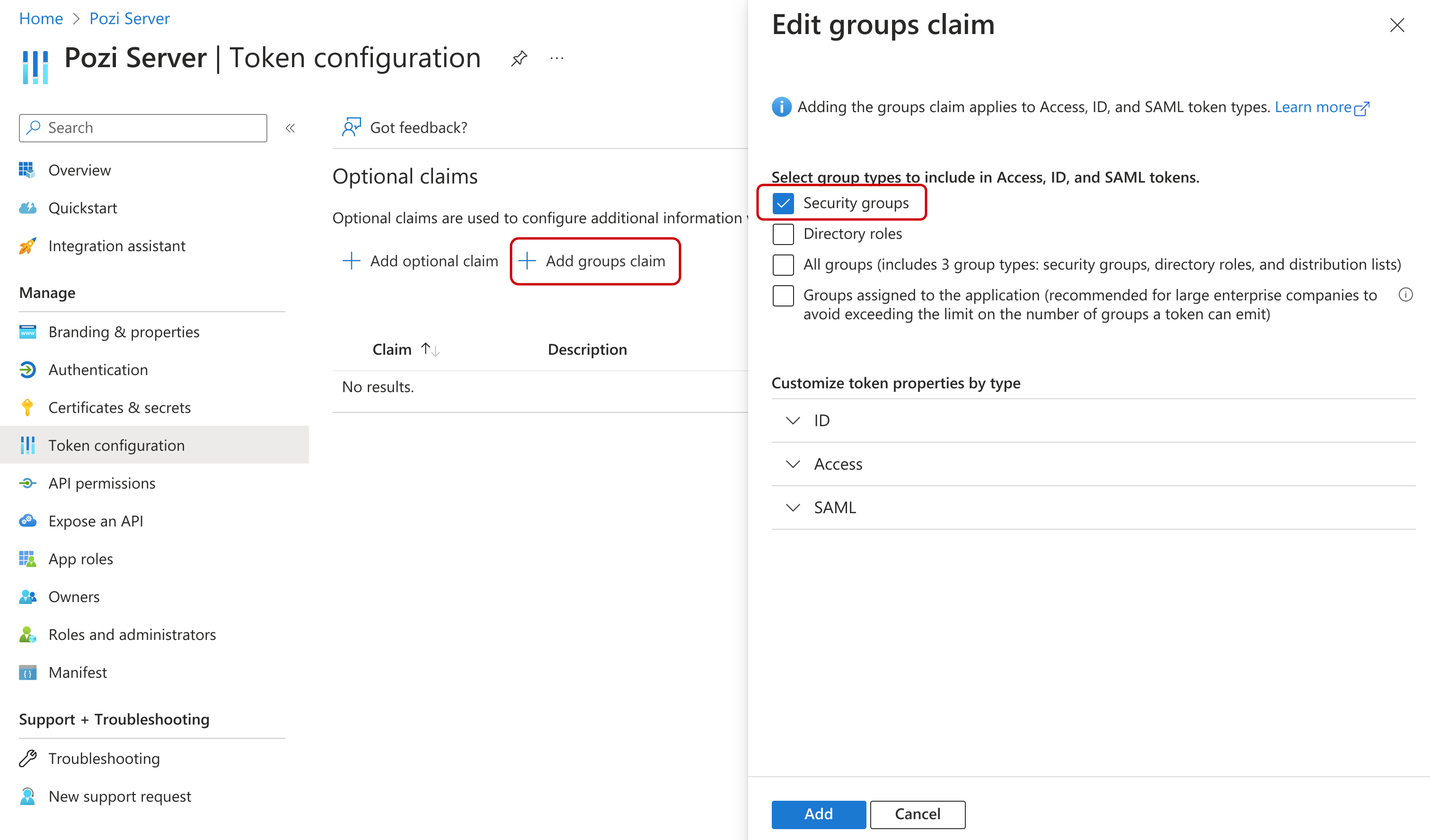
Go to the 'Token configuration' section and click on 'Add groups claim'. Then, select desired group types (just 'Security groups` is generally sufficient) and keep default settings
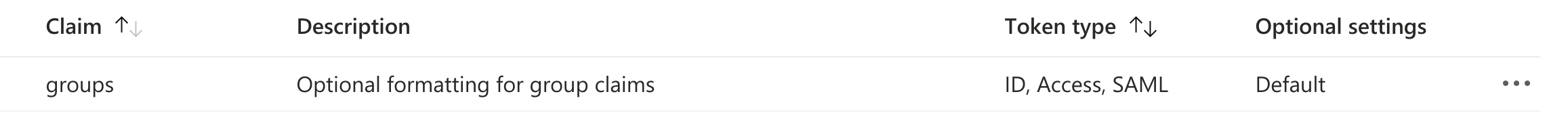
That is all that is needed in Entra ID. Pozi Web App will receive the group information as a list of group ids, like this:
"groups": [
"81ddec0b-6a1a-426a-9826-e869eef6473f",
"17b3a8a0-bc11-4ec3-810e-94c74201b41e",
"5ee9c710-26aa-40be-90be-36afa6fc2003",
"3adf8e2e-7628-41ee-b902-b105f231758e",
"c034a6cd-2b7d-4336-9f9e-9bb896ad1110"
]Email support@pozi.com with your list of group ids and what catalogues (ie QGIS projects) each group should have access to.
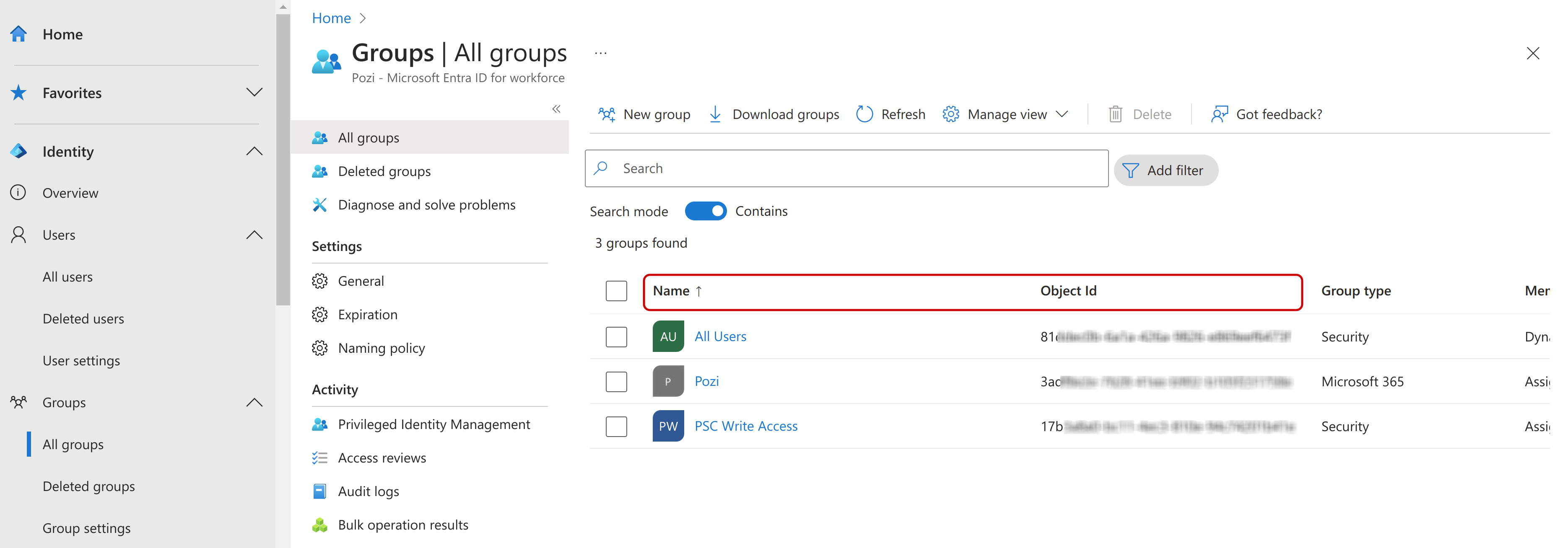
The group ids can be found under Identity ⇒ Groups ⇒ All groups.